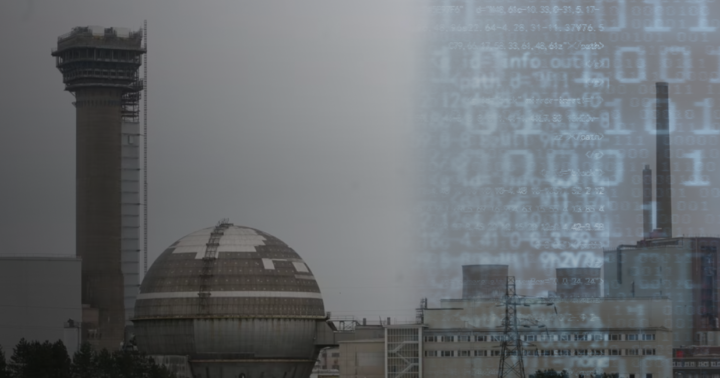
The Sellafield nuclear waste processing and storage site in the UK is under cyber threat. What is the risk of information leakage from the nuclear complex?
What happened?
Hackers with close ties to Russia and China have attacked the networks of the British nuclear complex Sellafield.
The Guardian's Nuclear Leaks investigation reports this.
The journalists found that the authorities do not know when the attackers first hacked into the site's IT systems. Senior staff at the nuclear waste storage facility concealed information about the hacking and its consequences.
However, according to The Guardian's sources, the hack was first detected in 2015.

Back then, unknown persons embedded suspicious software in Sellafield's computer networks.
The extent of the problem was revealed when Sellafield's external contractors could access the servers and notified the Office for Nuclear Regulation (ONR).
Sources in the ONR and security services said that Sellafield was subject to special measures due to "persistent cyber security breaches". However, the authorities declined to comment on the nature of the breaches.
"Some specific issues are the subject of ongoing investigations, so we cannot comment," an ONR source said.
How did Sellafield react to the investigation?
The nuclear complex's press service responded to the investigation. It said it "has no records or evidence to suggest that networks at the Sellafield nuclear site were the victim of a successful cyber attack by state actors in the manner described by the Guardian".

"Critical networks that enable us to operate safely are isolated from our general IT network, meaning an attack on our IT system would not penetrate these," the British government said in a statement published on its website.
Concerns over cyber security at a nuclear site
The Guardian reviewed a 2012 report that shows senior officials were aware of cyber issues at the nuclear site.
According to the report, security resources at the time were "insufficient to control the internal threat [from staff] ... let alone respond to the significant increase in external threats".
More than a decade after the report, Sellafield employees, regulators and sources in the intelligence community believe that the information systems at the nuclear waste site are still not secure.

Journalists' sources believe that senior management deliberately tried to hide the extent of the problems.
Security officials are also concerned that ONR is not rushing to share information about cyber failures at Sellafield, as they point out that controls have been ineffective for more than a decade.
In the 2023 report, the ONR notes Sellafield Ltd's success in cyber security but notes that the issue remains at the level of significantly increased attention from the regulator.
What is the risk of an information leak?
Sellafield is a nuclear complex located on the Irish Sea coast near Seascale. Its construction began in 1947. The facility used to produce plutonium for nuclear weapons during the Cold War and received radioactive waste from other countries.
Sellafield currently stores approximately 80% of the UK's nuclear waste.
The Labour Party's shadow secretary of state for energy security, opposition politician Edward Miliband, considers the information about the hack "a very concerning report about one of our most sensitive pieces of energy infrastructure".

"The government has a responsibility to say when it first knew of these allegations, what action it and the regulator took and to provide assurances about the protection of our national security," Miliband said.
In the ONR investigation, according to journalists' sources, Sellafield's server network was described as "fundamentally insecure".
Among the confidential documents stored at Sellafield are emergency manuals, nuclear protocol plans and instructions on what the UK would do in the event of a foreign attack.
The documents include the results of various exercises, including the Reassure exercise that Sellafield conducted in 2005 and the regular OSCAR exercise, which takes place every three years to test the effectiveness of emergency measures in the event of a radiation accident at the site.
Cyber attacks do not mean the beginning of a nuclear war, but they carry some risks:
- theft of materials from the facility, including those related to the production of nuclear weapons
- sabotage at a nuclear facility;
- potential access to command, control and communications systems.

The stolen secret information about nuclear facilities will allow attackers to sell this data to potential adversaries, which puts nuclear security at risk.
The Guardian's sources in the British security service say that cyber attacks and cyber espionage, particularly from Russia and China, are a growing threat to the UK.


